Authenticate callers in seconds with passkeys and MFA
Cut call handling time and stop fraud with our multifactor authentication solution designed to authenticate callers without disruption.



Protect every call with phishing-resistant authentication
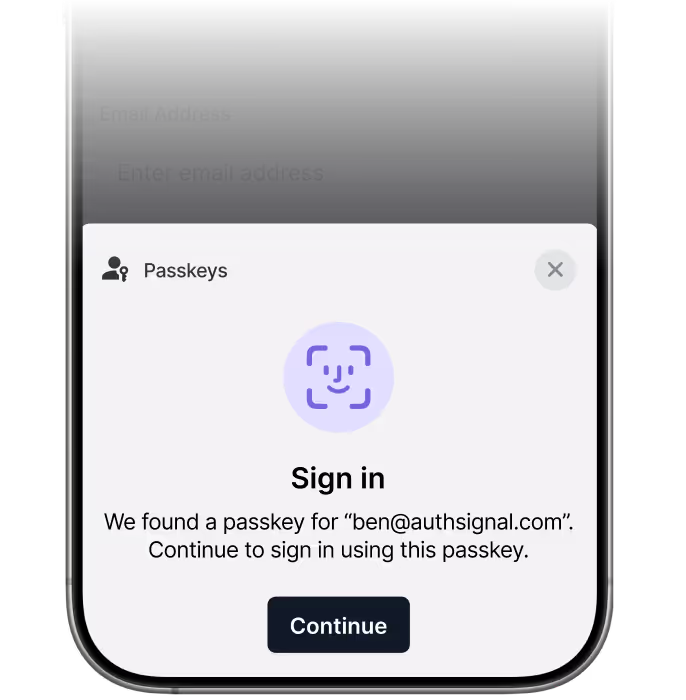
Verify callers instantly using passkeys, biometrics, push, WhatsApp OTP, or SMS, before agents handle sensitive requests. Integrates with ServiceNow, AWS Connect, and other major contact center platforms.
Lighting fast deployments
Drastically cuts call handle times
Mitigate fraud and social engineering
Trusted by leading businesses and built to integrate seamlessly












Key capabilities
Drop‑in verification for contact center
Deploy authentication into your call and ticket flows. Securely verify customer identity with passkeys, OTP, biometrics, and more

Omnichannel methods
Authsignal offers modern, phishing-resistant authentication like FIDO2 / Passkeys, plus flexible options including push, SMS, WhatsApp OTP, email links, and biometric verification.

Agent & workflow benefits
With Authsignal, agents can verify callers instantly, cutting handle times and keeping calls efficient.

No‑code rules
Ship policies fast; create rules and adapt to fraud patterns without developers.

Compliance‑ready
Authsignal is built with enterprise-grade security and meets the highest industry standards. We’re fully compliant with SOC 2 Type II, AICPA SOC, and FIDO Certified.

Audit & analytics
Gain full visibility into every user interaction with detailed, real-time event timelines. Track key actions like sign-ins, transaction attempts, challenges, and completions to support security reviews, fraud investigations, and compliance audits.

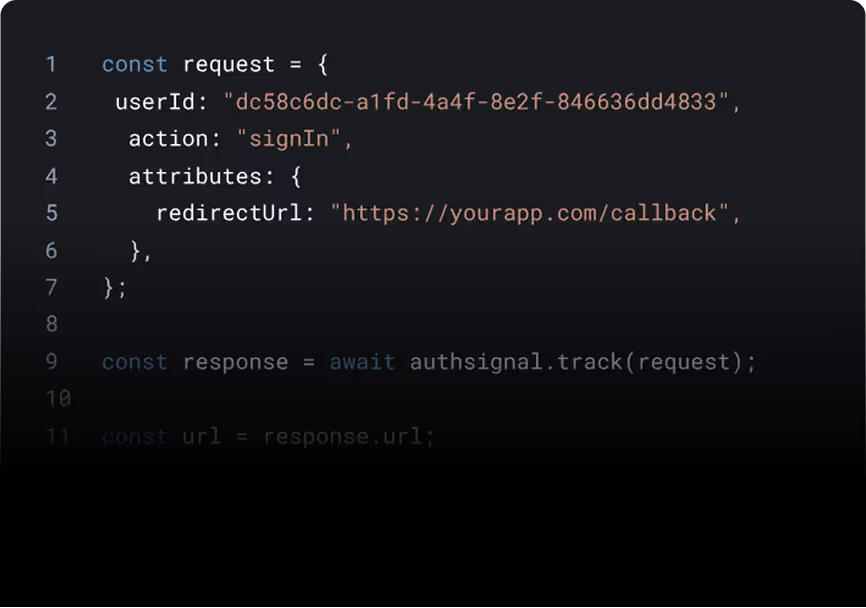
Developer‑friendly
Authsignal deploys easily with pre-built UI components, SDKs, and a flexible rules engine that integrates with existing contact center systems.
Get started with Authsignal
Book a demo with our team to see how Authsignal can secure and streamline authentication in your contact centre workflows.
Use cases
Account recovery / password reset
Verify the right person before unlocking or resetting access.
Verification caller identity
Step‑up auth for high‑risk privilege changes.
Sensitive ticket updates / closure
Require strong proof before closing or altering sensitive records.
High‑value transactions data access
Verify identity before exposing or moving sensitive data.
Answering your questions about contact center workflow and authentication
Yes. You can trigger verification from IVR flows (robot‑initiated) or let agents trigger it post‑call transfer. Both patterns are supported.
Most teams stand up a pilot in days. Pre‑built flows, SDKs, and a no‑code rules engine minimize custom work.
Passkeys (WebAuthn/FIDO2), push authentication, WhatsApp OTP, SMS OTP, and hardware security keys like YubiKey. You can mix methods per policy.
Yes. Replacing slow KBA with modern verification typically lowers AHT and removes escalations caused by uncertainty—without compromising security.
Authsignal is SOC 2 Type 2. Deployments can help support PCI DSS, ISO 27001, HIPAA, GDPR/UK GDPR, and PSD2/SCA requirements.








.png)
.avif)