Authsignal’s guide to minimising customer impact when deploying MFA.
Multi-factor Authentication (“MFA”), has been shown to block 99% of cyberattacks, far outperforming the simple, one-factor password protection. Today, many organisations are being pushed towards implementing MFA to meet compliance measures. Xero’s App marketplace now requires all partners to be MFA compliant. The Australian Tax Office is requiring those digital service providers who connect to their platform must now support MFA for both internal users and customers. From a business’ perspective, it’s a no-brainer to adopt MFA and increase your clients’ security. Across the industry, there has been an increase in consumer fraud and personal loss due to scams, all due to poor security measures and data breaches. Yet, for many website users, the value and safety that comes with passwordless authentication is eclipsed by the UX friction created by having those extra protection measures in place.
Customising Multi-factor Authentication Implementation to Reduce Friction
As businesses, we should always strive to tailor our services to our customer segment. When it comes to MFA, ethnicity, age group, and income brackets significantly impact customer familiarity and usage rates. For example, 69% of 18-24-year-olds are using MFA, compared with just 36% of those aged 55-64. Depending on your service and your customer, introducing the MFA at the login stage or too frequently may cause too much friction and hinder adoption. For that reason, Authsignal offers the flexibility to be able to deploy MFA anywhere along the customer journey, not just at the login stage. Our MFA software can be installed as a challenge to certain customer actions, as a setup authentication or could be limited to higher risk transferrals where a transaction exceeds a specific size or volume – lessening overall friction points for customers.
Increasing Customer Adoption
Fundamentally, at the core of customer hesitation around MFA adoption is psychological bias. Our ancient Neanderthal brains – which were highly useful in helping us survive centuries of living in the wilderness and escaping predators – just haven’t evolved fast enough to comprehend the unseen risks of the internet. To help adoption, we both need to make sure the MFA is as frictionless as possible, but we also need to harness persuasive language and design in our websites to override those biases. For example, the status quo bias (also known as the psychological inertia effect), means that as human beings, we have developed a preference towards business as usual and are reluctant to make changes if we believe our current systems are working sufficiently well. We understand that underlying this bias is a need to maintain control, which means that when we persuade customers to adopt MFA, we need to increase the stakes of continuing along the same course of action. Instead of promoting how MFA will increase a client’s level of protection, we could subtly reframe the ask as one where a client can opt to ‘keep control’ of their account.
Flexibility
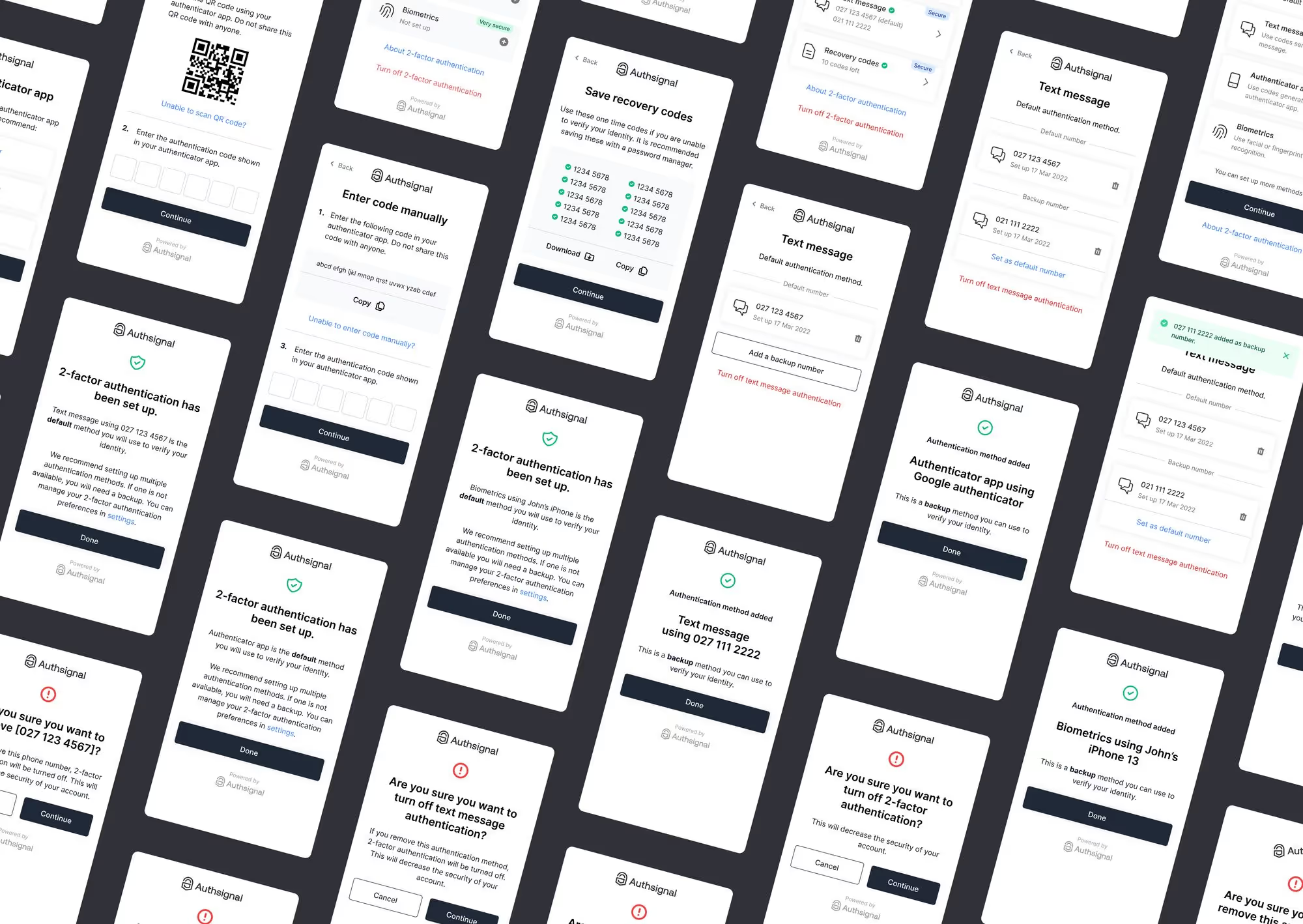
Approaching deployment with a flexible pathway to adoption in the early stages of introducing MFA / two-factor authentication is vital to a positive customer experience. Enabling your customers to increase the security of their accounts while not making multi-factor authentication compulsory initially is one approach that can lead to gradual and steady adoption. This approach requires that your MFA vendor supports a flexible deployment. Lastly, consider introducing MFA on a particular flow of your customer journey that is a higher risk or more sensitive touch point. e.g. changing bank accounts or a withdrawal flow. You can leverage in-app messaging, requesting the customer to further enhance the security of their account for withdrawals requiring them to turn on MFA. Click through to learn more on Authsignal’s suite of tools that can help you successfully manage the deployment of set-up authentication.
.svg)






.png)